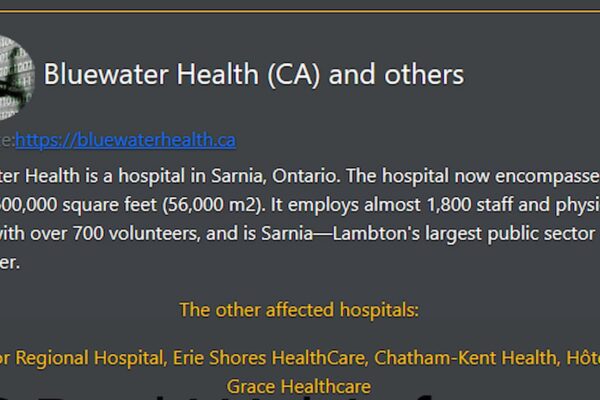
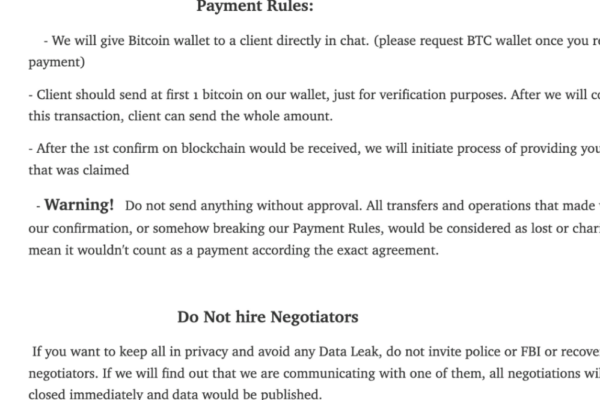
Daixin’s Ransomware Attack Paralyzes Five Ontario Hospitals
The Daixin team, notorious for targeting the public health sector, leaves five Ontario hospitals crippled in its latest ransomware attack.
The Daixin team, notorious for targeting the public health sector, leaves five Ontario hospitals crippled in its latest ransomware attack.

Kaspersky’s Q3 APT report showcases attacks involving secure USB drives, the emergence of “BadRory”, and the relentless offensive attack of North Korea’s Lazarus Group.
An international operation captures a ransomware developer and shuts down the dark web portal of Ragnar Locker.

Learn about the main types of password attacks, including brute force, password spraying, dictionary attacks, hash cracking, and rainbow table attacks.

Network beaconing allows malware to whisper stolen data to hackers while remaining invisible to our digital defenses.

Cybersecurity’s colorful teams collaborate to find weaknesses and defend against threats.

Breaking down the differences in driver manipulation attacks and why they pose such a serious threat to modern operating systems.

Explore the methods hackers use to secretly monitor your online actions, and get to know the security measures that work tirelessly to keep you safe.

The WiFi Coconut’s simultaneous monitoring of all 14 channels provides a unique and powerful tool for comprehensive passive WiFi reconnaissance and analysis.